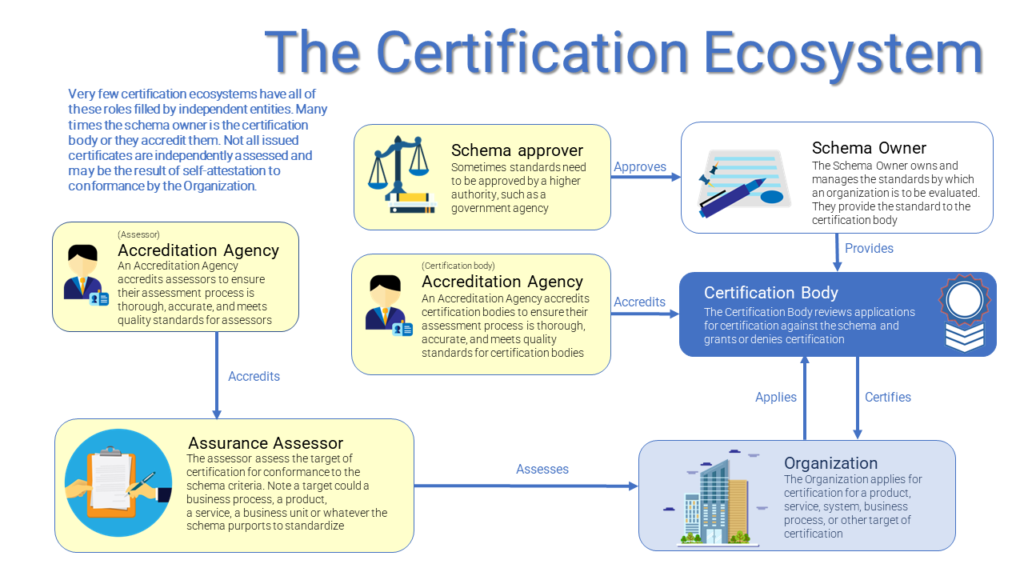
I’ve learned a lot about certification in that two years as I planned, researched and began to identify the steps best course of action to create this institute. While different certifications across industries apply different terms, I’ve tried to consolidate a common description of the “certification” ecosystem. At the core, you have some organization that wants to get something (often referred to as the target or object) certified and an entity or body that provides the certification. Beyond that are various organizations meant to ensure the certification offered is not done so in a perfunctory manner, in order to maintain the integrity of the certification. Here are some of the most common roles in the certification ecosystem:
- Organization/Applicant – The Organization applies for certification for a product, service, system, business process, or other target of certification
- Certification Body – The Certification Body reviews applications for certification against the schema and grants or denies certification. The role of the certification body is limited to assess the four corners of the application, not to assess the conformance of the organization to the standard. In other words, if the standard criteria says “The organization must have at least five employees” and the application for certification says the applicant has ten employees, the certificate is issued. Many certification bodies play the role of assessor (see below). An assessor would actually check the payroll of the applicant and assess that the application is accurate and the applicant actually has more than five employees. In that case, the entity is playing two roles: that of certification body, issuing the certification, and that of assessor, assessing the conformance of the applicant to the standard.
- Assurance Assessor – The Assessor assess the target (sometimes called the object of evaluation) of certification for conformance to the schema criteria. Note a target could a business process, a product, a service, a business unit or whatever the schema purports to evaluate. When an Assessor is not the issuing Certification Body, typically they are trained, approved or otherwise sanctioned by the Certification Body, who is relying on the accuracy of their assessment.
- Accreditation Agency (Assessor) – An Accreditation Agency accredits assessors to ensure their assessment process is thorough, accurate, and meets quality standards for assessors. Sometimes this is the Certification Body, but in more mature certification mechanisms this may be a distinct entity. Accreditation need not be to the particular standard the applicant is applying, but may be to more general qualities (such as security assessments or financial assessments). Many assessors may themselves be certified as compliant with ISO 9001 for quality management in their assessment process, thus the issuer of that certification to the assessor would be in the role of Accreditation Agency.
- Accreditation Agency (Certification Body) – An Accreditation Agency accredits certification bodies to ensure their accreditation process is thorough, accurate, and meets quality standards for certification bodies. Similar to the Accreditation Agency above, the accreditation of the certification body is likely not specific to the standard(s) they are certifying.
- Schema Owner – The Schema Owner owns and manages the standards or criteria by which a target or object is to be evaluated. They provide the standard to the certification body.
- Schema Approver – Sometimes standards need to be approved by a higher authority, such as a government agency.
To the best of my knowledge, no certification mechanism has distinct entities in every role. Some entities often hold multiple roles. Some of those may insulate their role from undue influence by having organizational firewalls or even separate legal entities. Here would be an example for ISO 27001 .
| Certification Schema | ISO 27001 Information Security Management System |
| Schema Owner | ISO/IEC JTC 1/SC 27 Joint Technical Committee/Standards Committee on Information security, cybersecurity and privacy protection |
| Schema Approver | ISO National Bodies – standards much be approved by a 2/3rds majority of National Body members of ISO (such as ANSI in the United States) |
| Certification Body | British Standards Institute (BSI) Here is where things get interesting, BSI is also the National Body representing the United Kingdom within ISO, though presumably a different department within BSI performs these functions. |
| Accreditation Agency (Certification Body) | United Kingdom Accreditation Service (UKAS) – accredits BSI as a certification body for ISO 27001 |
| Assurance Assessor | In this case BSI also acts as the assessor, assessing the applying organization’s conformance with the schema. |
| Accreditation Agency (Assurance Assessor) | None |
Two more examples, below, contrast the Payment Card Industries’ mechanisms for conformance to the Data Security Standards and the Payment Application Data Security Standards. You’ll note that because of the smaller set of organizations and the wider ranging impact of payment application providers on the security in the bank card system, PCI maintains tighter control of that mechanism.
| Certification Schema | PCI DSS (Data Security Standard) | PCI PA-DSS (Payment Application Data Security Standard) |
| Schema Owner | PCI Standards Security Council | PCI Standards Security Council |
| Schema Approver | None, the owning entity (PCI SSC) is also the approver | None, the owning entity (PCI SSC) is also the approver |
| Certification Body | None. Assessments are submitted to applicants’ acquiring/merchant banks, who accept (or reject) the assessment | PCI SCC. Referred to as validated, not certified payment applications. “Although the Council reviews these reports for relevant quality assurance purposes, the Council does not independently confirm these reports or the data or information they contain, nor does the Council perform tests or analysis of applications, products, or their functionality, performance, suitability, or compliance.” speaks to the notion that Certification Bodies are not assessors ,but ministerial bodies issuing certification upon valid applications. |
| Accreditation Agency (Certification Body) | None | None |
| Assurance Assessor | Coalfire Systems, Inc. (Example) | Coalfire Systems, Inc. (Example) |
| Accreditation Agency (Assurance Assessor) | PCI Standards Security Council | PCI Standards Security Council |
As you can see, even fairly mature certifications may not have independent actors in each role. As a nascent certification, the planned role of the IOPD is to be the Schema Owner (we’re the entity developing and managing the standard) as well as the Certification Body (we will issue certifications). Eventually, as we mature, we would like to be accredited, possibly by ANAB, with is the American National Standards Institute accreditation board for certification bodies. Our plan is to allow both self-assessment and attestation by applicants and third party assessments by assurance assessors. This is similar to the Cloud Security Alliance (CSA) model which has STAR Level 1 for self-attestations and STAR Level 2 of third party audits for their various certifications. As a long term goal, we’d like to get the standards approved by the EDPB as recognized certifications for Article 25 Data Protection by Design and Default under GDPR.
We have a long road ahead and would love your help in getting there. If you’re interested in getting involved, please consider joining as an Ambassador, getting your organization to sponsor, or volunteering in other ways.